Feed cleverhans-blog [copy] http://www.cleverhans.io/feed.xml has loading error: cURL error 22: The requested URL returned error: 404
Feed Security (b)log [copy] http://securityblogru.livejournal.com/data/rss has loading error: cURL error 22: The requested URL returned error: 403 Forbidden
Feed [bodyawm] Богдан [copy] https://habr.com/ru/rss/users/bodyawm/articles/?fl=ru has loading error: cURL error 22: The requested URL returned error: 404
Using Nix without the Nix: a Retrospective on Zilch (lixcon2026)

It's been a while since I last talked about Zilch; and now with Lix's existence, it's time to take another look; what's the status of this mysterious project, and what lessons can we learn from it?
Licensed to the public under http://creativecommons.org/licenses/by/4.0
about this event: https://pretalx.dgnum.eu/lixcon-2026/talk/QFSZRU/
Video:lixcon2026-14-eng-Using_Nix_without_the_Nix_a_Retrospective_on_Zilch_hd.mp4
To sleep in a sea of Tests | Refactoring a testing "framework" from hell (lixcon2026)

Taking a look at the `functional` test suite, pointing out its concepts and flaws to then take a look at its successor `functional2`
Many curses and screams of frustration has the functional test suite brought forth in many - if not all - lix developers. Hence people wanted a successor.
In this session, we will talk about all the pain, impurities and falkeyness of the functional suite, look at the features and non-features of functional2, and the pain of migrating tests.
Licensed to the public under http://creativecommons.org/licenses/by/4.0
about this event: https://pretalx.dgnum.eu/lixcon-2026/talk/KBFUXL/
Video:lixcon2026-1-eng-To_sleep_in_a_sea_of_Tests_Refactoring_a_testing_framework_from_hell_hd.mp4
Botanix: A Nix native CI in a forge-agnostic world (lixcon2026)

Botanix is a new CI software that targets a native nix integration as it builds derivations as its pipeline. It integrates natively with both Gerrit and Forgejo currently but its genericity allows for even more diversity in the future!
This talk will present the genesis of the Botanix project, worked on by students from ENS de Lyon, its philosophy and inner workings.
Licensed to the public under http://creativecommons.org/licenses/by/4.0
about this event: https://pretalx.dgnum.eu/lixcon-2026/talk/YZZKYT/
Video:lixcon2026-8-eng-Botanix_A_Nix_native_CI_in_a_forge-agnostic_world_hd.mp4
Nix and buck2: from enemies to lovers with snowydeer (lixcon2026)

Nix does dependencies and distribution well, but has a controlling personality: it wants to build everything in the build graph. Buck2 delivers fast, user-friendly, and scalable project builds, but has an equally controlling personality and a lacking public dependency ecosystem. What if their build graphs touched ... and they were both girls? In this talk, I will demonstrate how we go from Nix to buck2 to Nix then deploy with containers: * Using Nix for dependencies in buck2 * Using buck2 in the project build: remote caching, fast builds, ~zero evaluation time * Importing store paths to Lix from buck2...
Human Trust of AI Agents
Interesting research: “Humans expect rationality and cooperation from LLM opponents in strategic games.”
Abstract: As Large Language Models (LLMs) integrate into our social and economic interactions, we need to deepen our understanding of how humans respond to LLMs opponents in strategic settings. We present the results of the first controlled monetarily-incentivised laboratory experiment looking at differences in human behaviour in a multi-player p-beauty contest against other humans and LLMs. We use a within-subject design in order to compare behaviour at the individual level. We show that, in this environment, human subjects choose significantly lower numbers when playing against LLMs than humans,...
Defense in Depth, Medieval Style
This article on the walls of Constantinople is fascinating.
The system comprised four defensive lines arranged in formidable layers:
The brick-lined ditch, divided by bulkheads and often flooded, 15-20 meters wide and up to 7 meters deep. A low breastwork, about 2 meters high, enabling defenders to fire freely from behind. The outer wall, 8 meters tall and 2.8 meters thick, with 82 projecting towers. The main wall—a towering 12 meters high and 5 meters thick—with 96 massive towers offset from those of the outer wall for maximum coverage.Behind the walls lay broad terraces: the parateichion, 18 meters wide, ideal for repelling enemies who crossed...
Android ohne Überwachung: FOSS-Apps auf dem Smartphone (glt26)

None Im Juli 2024 zeigte eine ausführliche Recherche von netzpolitik.org und dem Bayerischen Rundfunk anschaulich, wie Standortdaten detaillierte Bewegungsprofile von Millionen Menschen offenlegen. Viele Apps, darunter Wetter-, Navigations- oder Dating-Apps, senden diese Informationen an die jeweiligen Anbieter, sobald Nutzer die Standortfreigabe aktivieren. Solche Daten sind wertvoll und werden von Datenhändlern weiterverkauft. Wer die herkömmlichen Apps auf einem normalen Android-Smartphone nutzt, kann gegen diese Überwachung nur wenig tun. Es geht aber auch anders: Zahlreiche FOSS-Apps eignen sich durchaus als Alternative zu den bislang gewohnten Apps. Sie arbeiten meist datensparsam, sodass sich der digitale Fußabdruck verringert. Zudem bieten alternative...
grommunio - Bridging Reality: Open Source, Digital Sovereignty. Open Source, Not Open-Washed. (glt26)

None Wie digitale Souveränität in der Praxis tatsächlich funktioniert Open Source war noch nie so beliebt – und noch nie so missverstanden. In den letzten Jahren ist digitale Souveränität zu einem politischen Schlagwort geworden, Anbieter bezeichnen ihre Produkte stolz als offen, und doch fühlen sich Nutzer und Institutionen oft mehr denn je eingeschränkt. Hinter offenen APIs verbergen sich proprietäre Kerne, hinter „Alternativen” oft neue Abhängigkeiten und hinter glänzenden neuen Plattformen die gleichen alten Migrationsprobleme. Wie sieht echte digitale Souveränität tatsächlich aus – in der Produktion, im Alltag, unter realen Einschränkungen? Anhand des konkreten Beispiels von grommunio zeigt dieser Vortrag,...
Neues Monitoring-System der Systemlandschaft der Grazer Linuxtage (glt26)

None
Die Grazer Linuxtage wollten für ihre Systemlandschaft ein Monitoring-System. Zwei Schüler der HTBLA Kaindorf haben dies im Rahmen ihrer Diplomarbeit umgesetzt. In diesem Vortrag wird das System kurz vorgestellt, welche Technologien eingesetzt wurden und was sie dabei genau gemacht haben.
Licensed to the public under https://creativecommons.org/licenses/by/4.0/
about this event: https://pretalx.linuxtage.at/glt26/talk/87Y9UQ/
Video:glt26-621-deu-Neues_Monitoring-System_der_Systemlandschaft_der_Grazer_Linuxtage_hd.mp4
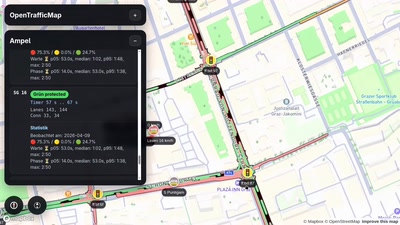
C-ITS: Mit einem ESP32 Ampeln, Straßenbahnen und Autos tracken (glt26)
None Wusstest du, dass dein Auto, wenn es **Car2X** über **ITS-G5** unterstützt, bis zu 4 mal pro Sekunde die exakte GPS-Position, Geschwindigkeit, Längs- und Querbeschleunigung, Pedalstellungen, Länge + Breite und vieles mehr unverschlüsselt auf einem 5-GHz-Band überträgt? Auch die Straßenbahnen in Graz senden diese Daten, und sogar ihre Liniennummer. Damit können wir die Garnituren live tracken und in einer Karte anzeigen. Viele Ampeln in Graz unterstützen mittlerweile **C-ITS** und senden sekündlich Daten über den genauen Aufbau der Fahrstreifen und den exakten Zustand der Signale, sowie wann die nächste Phase zu erwarten ist. Mit einem **ESP32-C5** können wir diese...