Feed cleverhans-blog [copy] http://www.cleverhans.io/feed.xml has loading error: cURL error 22: The requested URL returned error: 404
Feed Security (b)log [copy] http://securityblogru.livejournal.com/data/rss has loading error: cURL error 22: The requested URL returned error: 403 Forbidden
Feed [bodyawm] Богдан [copy] https://habr.com/ru/rss/users/bodyawm/articles/?fl=ru has loading error: cURL error 22: The requested URL returned error: 404
No Magic, Just Modbus – Einführung in die OT-Sicherheit (eh23)

OT (Operational Technology) ist nicht nur IT mit dickeren Kabeln.
Dieser Talk führt in das Thema Sicherheit in industriellen Steuerungssystemen ein und zeigt, wie man Angriffe mit Frameworks strukturiert analysieren und einordnen kann.
Und ganz nebenbei klären wir, warum Kraftwerke im Kino deutlich schneller explodieren als in der Realität.
Einsteigerfreundlich, keine besonderen Vorkenntnisse erforderlich. ^^
This work is licensed under CC BY-NC 4.0. To view a copy of this license, visit https://creativecommons.org/licenses/by-nc/4.0/
about this event: https://pretalx.eh23.easterhegg.eu/eh23/talk/RVCZAU/
Video:eh23-103-deu-No_Magic_Just_Modbus_-_Einfuehrung_in_die_OT-Sicherheit_hd.mp4
EscapeRoom im Wohnzimmer - und hunderte sind via Kamera dabei... (eh23)

Wir, zwei Wesen aus Wuppertal, haben während der Pandemie einen EscapeRoom zum Thema "Mittelalter & Drachen" im halben Wohnzimmer gebaut, und dann digital (via Kamera aufm Kopf und Zoom) Kinder- und Jugendlichengruppen zum Rätseln reingelassen (Vereinsprojekt). Aus "ach komm, ein Adventswochenende reicht, so viele machen da nicht mit" wurde dann "die Anmeldeseite ist abgestürzt!", hektisch-spontane Zusatztermine bis Karneval neben dem Job, und auch später immer mehr Nachfragen "Macht ihr das nochmal?" Toll: Positivstes Feedback, relativ gut beim Thema Barrierefreiheit (danke hier an unsere Experten zu den Bereichen Hörschädigung, Seheinschränkung, Mobilitätsprobleme, Epilepsie,..), innervereinlich schlagartig bekannt....
Elektronische Schlüssel Profilfräsen, mach deinen Schlüsselrohling doch selbst. (eh23)
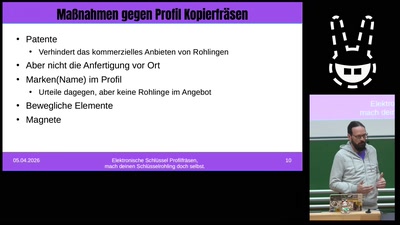
Der Schlüsselkopierschutz von Schließanlagen basiert darauf, das man die entsprechenden Schlüsselrohlinge nicht bekommt. Wie fräst man einen passenden Schlüssel aus einem Vollbart Rohling, von dem ersten modifizierten Orginal Schlüssel, über rein mechanischen Fräsen, zu selbstgebauten Profilfräsen. Eine tiefe Analyse des ersten kommerziell erhältlichen elektronischen Profilfräßautomat und lustigen Entdeckungen in der Firmware. Wie kommt man vom Foto des Schließzylinders zum passenden Schlüssel. Was für Gegenmaßnahmen ergriff die Schlossindustrie, und warum klappt es trotzdem Eine interessante Reise durch mechanische Sicherungssysteme und interesannte Maschinenkonstruktionen. Über einen kurzen Überblick über Profil Variation verschiedener Schließanlagen, über die Anfänge von Profil...
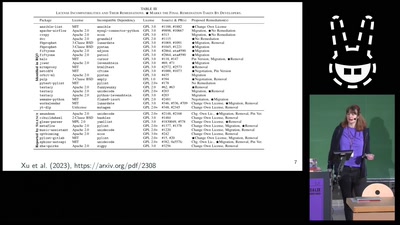
The Paper is a Lie: Practical Data Forensics for Scientific Data (eh23)

Recent high-profile cases of scientific fraud have demonstrated that scientists are only human too and sometimes individual scientists falsify their data. Since science is the basis of decision- and policy-making, we all should be able to scrutinise scientific studies. Here, we provide practical guidance and concrete tools for forensically examining scientific data and identifying potential cases of data manipulation. These approaches will enable and empower audience members to independently perform forensic plausibility checks on scientific data, as well as provide a starting point for their further, independent study. Limitations and ethical considerations when performing...
Open Source Lizenzen: Wenn die Welt in Belgien zuhause ist und andere Absurditäten (eh23)
Wir erzählen euch etwas über Open-Source-Lizenzen, ob sie so funktionieren wie gedacht und andere Absurditäten. Alle reden von Open Source. Wir nicht. Wir reden über Open-Source-Lizenzen! GPL haben alle wohl schonmal gehört. Aber was macht diese Lizenz genau? Ist dynamisches Linken eine mögliche Umgehung, gibt es da was anderes? Was macht diese Lizenzfamilie überhaupt? Was gibt es sonst noch für Open-Source-Lizenzen? Was ist die EuPL, die LiLiQ-R+ oder auch die MPL? Und warum ist die Welt (manchmal) in Belgien zuhause? Wir möchten euch eine Führung durch die Welt der Open-Source-Lizenzen und ihre Absurditäten geben, weil...
How NOT to IPv6 (eh23)

Ein buntes Potpourri an Worst-Practices wie man die IPv6 Einführung nicht schafft. Die Transition des Internets von IPv4 zu IPv6 dauert jetzt schon weit über 20 Jahre, trotzdem geht sie in einigen Bereichen nur schleppend voran. In diesem Talk möchte ich einige Worst-Practices vorstellen, die auf den ersten Blick für Manche nach einer guten Idee aussehen, aber den Weg zu IPv6 der eigenen Organisation wirksam versperren, und ein paar Wege aus diesen Sackgassen aufzeigen. Nicht alle sind selbst erprobt bzw. bis zum Ende beschritten, aber alle illustrierten, dass die Transition zu IPv6 meistens nich an technischen...
Warum sind hier überall Seile? Seilbahntechnik für Nerds! (eh23)

Die Seilbahn zur Festung Ehrenbreitstein ist aus Koblenz kaum noch wegzudenken. Doch wie ist es dazu gekommen? Woher kommt die Seilbahntechnik, wie funktioniert sie und ist das überhaupt sicher? Was sind Pendel-, Einseilumlauf-, 2S- und 3S-Bahnen? Oder Funitel und Tri-Line? Und können wir die auch für den öffentlichen Personenverkehr gebrauchen? Ausnahmsweise reden wir mal nicht über die Eisenbahn, sondern nehmen euch passend zum diesjährigen Austragungsort der Easterhegg mit auf eine Reise in die Luft und geben eine Einführung in die Seilbahntechnik für Nerds! Warum hängen hier überall Seile? Diese Frage wurde schon bei so mancher Chaos-Veranstaltung gestellt...
E-Mail selbst hosten - Zwischen DNS, Spamfiltern und Big Tech (eh23)
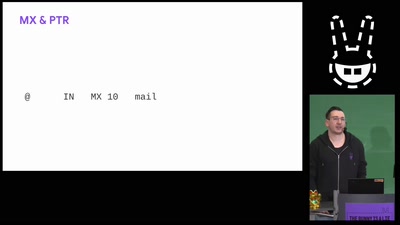
E-Mail gilt als kompliziert und kaum selbst betreibbar. Trotzdem ist es das größte wirklich dezentrale Kommunikationsmittel. Dieser Talk ist ein Realitätscheck für technisch versierte Menschen mit Hosting-Erfahrung, die sich bisher nicht an einen eigenen Mailserver herangetraut haben. Wir schauen uns an, wie E-Mail heute tatsächlich funktioniert, warum Reputation wichtiger ist als Software und weshalb das größte Problem beim Mailhosting kein technisches, sondern ein soziales ist. Der Talk richtet sich an interessierte Hacker, die ihre Mails selbst hosten wollen und sich ggf. bis jetzt getraut haben, vielleicht auch weil sich Reddit einig ist, dass man Mail...
Inhalt irrelevant - Was sagen deine Metadaten? (eh23)
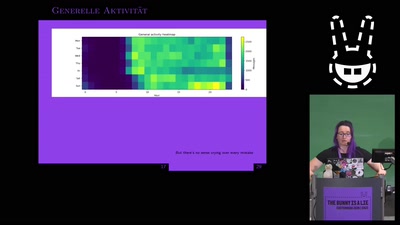
Verschlüsselung von privaten Chatnachrichten ist nur ein kleiner Teil einer Sicherheitsmaßnahme zum Schutze der eigenen Privatsphäre. Welche intimen Informationen auch ohne den Inhalt von spicy Nachrichten erkennbar sind, schauen wir uns in diesem Talk an. Nachrichten sind sicher und privat, denn sie sind nach aktuellen Verfahren verschlüsselt und liegen sicher auf unseren Servern! So könnte die Behauptung von Anbietenden von Nachrichtendiensten lauten. Doch wie privat ist das eigene Leben wirklich, wenn wir uns einfach nur anschauen, wann wir mit wem welche Nachrichten austauschen? Inhalt irrelevant, wir interessieren uns lediglich für alle intimen Informationen über das...
Embedded Engineering – Wenn dein Code direkt mit der Welt spricht (eh23)

Web-Apps und Desktop-Tools hat jedes IT'wesen schon geschrieben – aber was, wenn dein Code direkt LEDs, Motoren oder Sensoren steuert? In diesem kurzen Vortrag tauchen wir in die Welt der Embedded-Systeme ein: kleine Computer ohne Betriebssystem, direkt auf der Hardware, aber mit moderner Sprache und solider Architektur.
Mit einem Mix aus Coding, Praxisbeispielen und technischen Einblicken zeige ich dir, wie Embedded-Entwicklung mit Rust nicht nur sicher, sondern auch richtig spannend wird.
This work is licensed under CC BY-NC 4.0. To view a copy of this license, visit https://creativecommons.org/licenses/by-nc/4.0/
about this event: https://pretalx.eh23.easterhegg.eu/eh23/talk/PK9R9Z/
Video:eh23-20-deu-Embedded_Engineering_-_Wenn_dein_Code_direkt_mit_der_Welt_spricht_hd.mp4