Feed cleverhans-blog [copy] http://www.cleverhans.io/feed.xml has loading error: cURL error 22: The requested URL returned error: 404
Feed Security (b)log [copy] http://securityblogru.livejournal.com/data/rss has loading error: cURL error 22: The requested URL returned error: 403 Forbidden
Feed [bodyawm] Богдан [copy] https://habr.com/ru/rss/users/bodyawm/articles/?fl=ru has loading error: cURL error 22: The requested URL returned error: 404
Warum klappt die Auskunftsapp nie dann, wenn man sie mal braucht? (eh23)

Warum zeigt die Auskunftsapp schon wieder eine falsche Prognose an? Warum verschwindet eine Verspätung plötzlich oder taucht doppelt auf? Anhand eines alltäglichen Ausnahmeereignisses führt dieser Vortrag in die oft unsichtbare Welt der ÖPNV-Auskunftssysteme in Deutschland ein. Verspätung weg, Gleis geändert, Fahrt fällt aus und fünf Minuten später zeigt die App plötzlich wieder etwas völlig anderes an. Zufall? Schlechte App? Oder steckt dahinter ein System, das unter Ausnahmezuständen an seine Grenzen stößt? Dieser Talk nimmt euch mit hinter die Kulissen der ÖPNV-Auskunft in Deutschland. Ausgehend von einem realen Ausnahmeereignis schauen wir uns an, wie Fahrgastinformationen eigentlich entstehen:...
Gemeinsame Reise durch deutsche Behördendomains (eh23)
In vielen Ländern sind staatliche .gov-Domains längst Standard - etwa gov.uk. In Deutschland dagegen sind gov.de oder bund.de bei staatlichen Stellen deutlich weniger verbreitet, als man erwarten würde. Stattdessen existieren historisch gewachsene Sonderlösungen: Ministerien mit eigenen Domains, Umbenennungen nach Regierungswechseln, ein insgesamt inkonsistentes Namensschema und noch mehr Verwirrung bei Domains auf Landesebene. In diesem Talk schauen wir uns die kuriosesten Ausprägungen dieses Domain-Chaos an, analysieren ihre praktischen Auswirkungen und diskutieren, wie es gemeinsam besser gehen könnte. Dabei werfen wir auch einen Blick auf Security-Fails, die aus genau diesen Strukturen entstehen können. Behördendomains reloaded: Von offenen...
Frequenzmessung unhörbarer Signale (eh23)

Vier Amateurfunk-Kurzwellensignale. Laut Ankündigung müssten sie da sein, aber zu hören ist: Nichts. Nur Rauschen. Trotzdem schaffe ich, von dreien dieser vier Signale die Frequenz auf ein Hz genau zu bestimmen! Ein persönlicher Bericht von einem Nerdvergnügen und nebenbei eine von vielen möglichen Antworten auf: "Was machen diese Funkamateure eigentlich so?" Zweimal im Jahr veranstalten Funkamateure in den USA eine Ostereiersuche der besonderen Art: Den [Frequency Measurement Test](https://fmt.arrl.org/). Auf vorher nur ungefähr bekannten Frequenzen im Kurzwellenbereich bei 3,5 und 7 MHz senden sie insgesamt vier Signale. Jedes dieser Signale stellt ein Osterei dar: Gefunden hat...
Warum sind hier überall Seile? Seilbahntechnik für Nerds! (eh23)

Die Seilbahn zur Festung Ehrenbreitstein ist aus Koblenz kaum noch wegzudenken. Doch wie ist es dazu gekommen? Woher kommt die Seilbahntechnik, wie funktioniert sie und ist das überhaupt sicher? Was sind Pendel-, Einseilumlauf-, 2S- und 3S-Bahnen? Oder Funitel und Tri-Line? Und können wir die auch für den öffentlichen Personenverkehr gebrauchen? Ausnahmsweise reden wir mal nicht über die Eisenbahn, sondern nehmen euch passend zum diesjährigen Austragungsort der Easterhegg mit auf eine Reise in die Luft und geben eine Einführung in die Seilbahntechnik für Nerds! Warum hängen hier überall Seile? Diese Frage wurde schon bei so mancher Chaos-Veranstaltung gestellt...
Inhalt irrelevant - Was sagen deine Metadaten? (eh23)
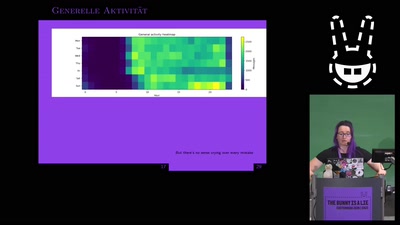
Verschlüsselung von privaten Chatnachrichten ist nur ein kleiner Teil einer Sicherheitsmaßnahme zum Schutze der eigenen Privatsphäre. Welche intimen Informationen auch ohne den Inhalt von spicy Nachrichten erkennbar sind, schauen wir uns in diesem Talk an. Nachrichten sind sicher und privat, denn sie sind nach aktuellen Verfahren verschlüsselt und liegen sicher auf unseren Servern! So könnte die Behauptung von Anbietenden von Nachrichtendiensten lauten. Doch wie privat ist das eigene Leben wirklich, wenn wir uns einfach nur anschauen, wann wir mit wem welche Nachrichten austauschen? Inhalt irrelevant, wir interessieren uns lediglich für alle intimen Informationen über das...
The Bunny is a Lie, but Rust is the Truth: High-Performance Modeling & APIs (eh23)
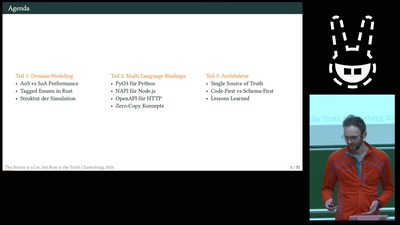
„Die API ist dokumentiert“, „Das JSON-Schema passt“ – oft sind das die größten Lügen in der Softwareentwicklung. Sobald Daten zwischen Rust-Kern, Python-Skripten und TypeScript-Frontends fließen, bricht das Chaos aus. In diesem Talk zeige ich euch, wie wir Rust als „Single Source of Truth“ nutzen, um mit Tagged Enums und automatisierter API-Generierung (OpenAPI/PyO3) den Kaninchenbau aus inkonsistenten Typen und Performance-Flaschenhälsen ein für alle Mal zu verlassen. Wer hat nicht schon mal Stunden damit verbracht, einen Bug zu suchen, nur weil das Python-Skript ein Feld erwartet hat, das im Rust-Backend nach dem letzten Refactoring umbenannt wurde? Oder...
Friday Squid Blogging: Jurassic Fish Chokes on Squid
Here’s a fossil of a 150-million year old fish that choked to death on a belemnite rostrum: the hard, internal shell of an extinct, squid-like animal.
Original paper.
As usual, you can also use this squid post to talk about the security stories in the news that I haven’t covered.
Blog moderation policy.
Company that Secretly Records and Publishes Zoom Meetings
WebinarTV searches the internet for public Zoom invites, joins the meetings, secretly records them, and publishes (alternate link) the recordings. It doesn’t use the Zoom record feature, so Zoom can’t do anything about it.
Pyth soars 9% following Polymarket integration. Will it rally higher?

Key takeaways
PYTH is up 9% in the last 24 hours, outperforming other major cryptocurrencies. The rally comes following Pyth Network’s integration with Polymarket.PYTH, the native coin of the Pyth Network, is one of the best performers in the crypto market over the past 24 hours. It could rally higher in the near term as the broader market recovers from Thursday’s slump.
PYTH rallies on Polymarket integrationOn Thursday, Pyth Network revealed in a blog post that Polymarket, the world’s largest prediction market platform, has integrated Pyth Pro as its data source for a new suite of traditional asset contracts.
The initial offerings include gold,...
Ether targets the $2,166 resistance as buyers step in

Key takeaways
ETH is up by less than 1% and now trades above $2,050. The bulls defended the $2,000 support level, with further upward movement on the card.Ethereum is up by less than 1% at the time of writing on Friday, halting the bearish performance that gripped the market on Thursday. The coin could rally higher in the near term as buyers have stepped in over the past few hours.
Onchain data paints a mixed picture for EtherETH is trading above $2,050 at press time, but onchain data paint a mixed picture for the top altcoin. Over the past week, investors across different...