Feed cleverhans-blog [copy] http://www.cleverhans.io/feed.xml has loading error: cURL error 22: The requested URL returned error: 404
Feed Security (b)log [copy] http://securityblogru.livejournal.com/data/rss has loading error: cURL error 22: The requested URL returned error: 403 Forbidden
Feed [bodyawm] Богдан [copy] https://habr.com/ru/rss/users/bodyawm/articles/?fl=ru has loading error: cURL error 22: The requested URL returned error: 404
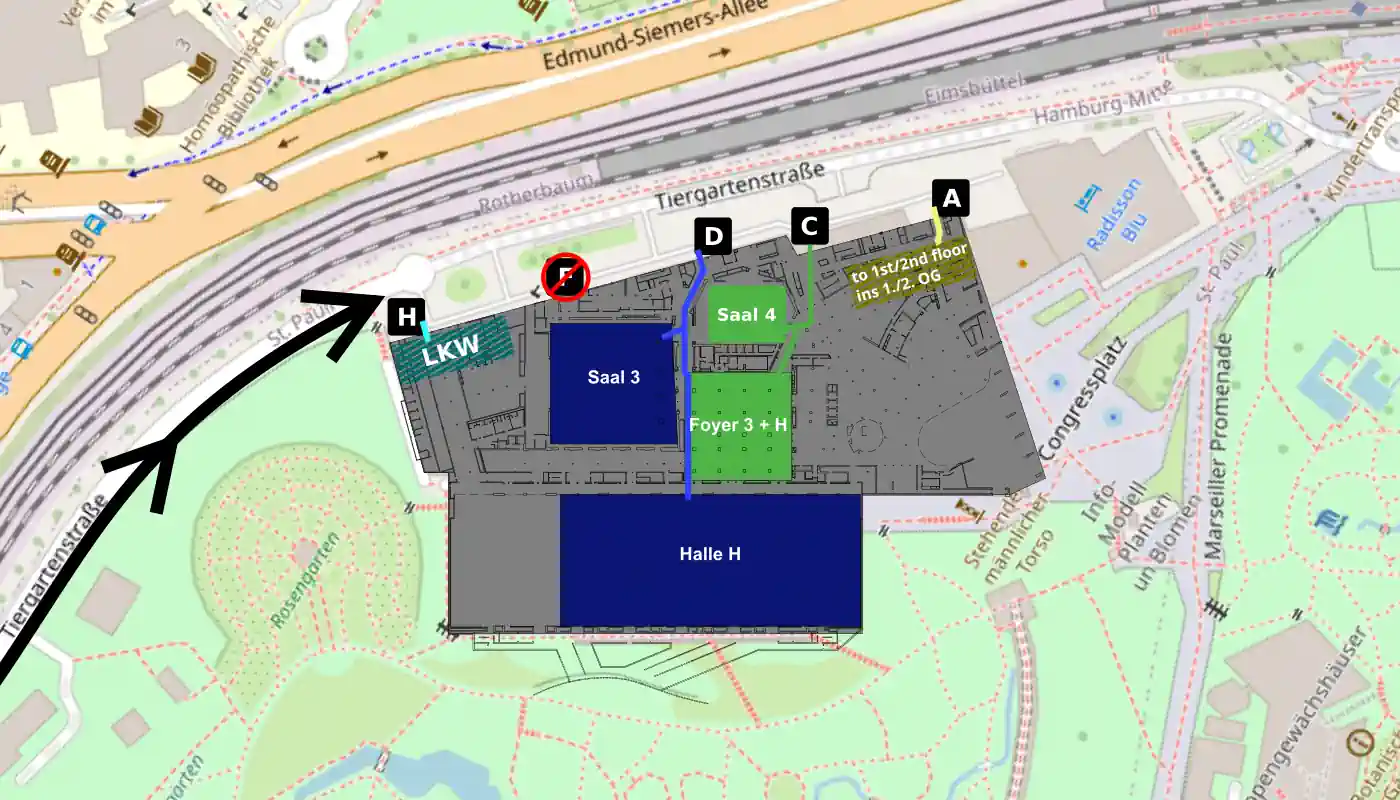
39C3: Power Off zur Abreise!
Liebe Wesen und Teilnehmende,
das Ende ist nahe! Tage voller Begegnungen, Neugier, Lötzinn, Diskurs, Musik, Code und Chaos liegen hinter uns. Danke, dass ihr diesen Congress mit Leben gefüllt habt. Ihr habt ihn zu dem gemacht, was er ist.
So sehr wir uns wünschen, dass der Congress ewig weiterläuft, kommt nun der Moment des Zusammenpackens, Durchatmens und Abschiednehmens.
Nach dem Closing beginnen die Assemblies damit, ihre Räume wieder zu leeren. Bitte nehmt euch die Zeit, ordentlich und achtsam abzubauen. Räumt möglichst schnell eure Tische frei, damit das Möbelhaus Tische und Stühle abtransportieren kann und Netzwerk und Strom abgebaut werden können. Die Hardware für...
Block Domains and Advertisements in a ZTE DSL Router

In one of my previous blog posts I showed how to install and run PiHole DNS server locally as a Docker container in your Synology NAS server. This worked great as the PiHole dashboard shows the list of identified annoying advert requests that were blocked shows.
So far I did configure my PiHole DNS server within my Chrome browser so that the browser cant load those annoying domains anymore. This worked like a charm, until quite recently Google updated Chrome browser to only allow a ‘secured DNS connection’ which actually seems a bit of a trojan horse for their own ads...
OpenTelemetry Astroshop Simulator
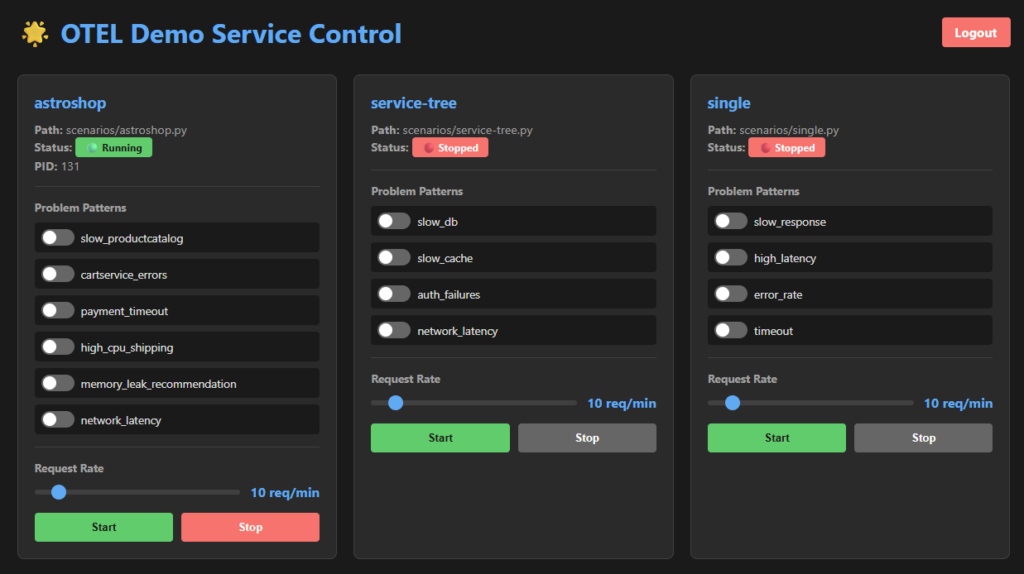
Astroshop is a great way of testing and running a demo scenario that offers with a large spectrum of technologies, services and a realistic problem scenario of running a real shop in serverless or Kubernetes infrastructure.
Besides, Astroshop being a great way to demo and test observability platforms such as Dynatrace and to run problem scenarios on demand, its also a bit cumbersome to deploy it for testing purposes. Imagine that you are a local developer that just needs to quickly run a test for a new feature using OTel traces and spans. Deploying Astroshop or any other scenario always comes...
ChaosPager: Teste unsere Pager‑Infrastruktur!
Du findest Pager toll? Dich interessiert, wie man eine kritische Infrastruktur konzipiert, oder du möchtest solche Systeme am 39C3 kennenlernen? Du suchst einen einfachen Einstieg in die Welt des Amateurfunks?
Wir vom Assembly Signalspielplatz entwickeln und betreiben in Kooperation mit dem CERT und der Funkergruppe DL0TUH eine Pagerinfrastruktur, die in Zukunft die Einsatzkräfte des CERTs alarmieren soll. Um diese zu erpoben, würden wir uns über viele Testaussendungen von euch freuen!
Nachrichten empfangenWir betreiben unser System auf 439.9875MHz. Folgende RICs stellen wir für euch bereit:
RIC Beschreibung 8 Sender-ID (DL0TUH) 1111 Info 1122 Tests 1140 Event-Info Saal Zero 1141 Event-Info Saal One 1142 Event-Info Saal Ground 1143 Event-Info Saal Fuse 1150 Event-Info alle Säle 2504 Datum & Zeit (Skyper)Bitte beachtet, dass wir im...
39C3: Telefonie
TL;DR Registrierung geöffnet – registriere deine Nummer im Guru3 Vergiss dein Telefon (ISDN, DECT, GSM, SIP) nicht Denk an Akkus, Ladekabel und CCC-SIM-Karte Es wird eSIMs für das GSM Netz geben Die Einwahl von außen lautet: +49 40 5730830 xxxx
Der Aufbau für den 39C3 ist bereits im vollen Gange. Ihr habt schon mehr als 5.600 Nebenstellen registriert. Unsere Vorfreude ist sehr groß. Wir möchten euch gerne über die Telefonie auf dem 39C3 informieren und haben die folgenden Details zu allen Technologien, mit denen ihr am Telefonnetz des Congress teilnehmen könnt, zusammengestellt. Wie im letzten Jahr wird es wieder einen Phone-Helpdesk geben, der euch bei...
GNUnet 0.26.2
GNUnet 0.26.2
This is a bugfix release for gnunet 0.26.1. It fixes some regressions and minor bugs.
Links Tarball download (tar.gz) ( signature )
You can find a detailed list of changes in...
39C3: Congress Everywhere
Auch in diesem Jahr bieten wieder Hackspaces und andere Orte die Möglichkeit, gemeinsam Vorträge zu streamen, zu hacken, Party zu machen und mehr. Der Congress ist überall, wo er gelebt wird. Dabei gibt es auch die Möglichkeit, sich gegenseitig zu besuchen.
Diese Congress-Everywhere-Orte sind uns bekannt:
Ort Veranstalter / Website Tag 1 / 27.12. Tag 2 / 28.12. Tag 3 / 29.12. Tag 4 / 30.12. Aachen CCCAC ab 11:00 ab 11:00 ab 11:00 ab 11:00 Basel (CH) CCC Basel ab 13:00 ab 13:00 ab 13:00 ab 13:00 Berlin berlinCreators e.V. ab 11 Uhr ab 12 Uhr ab 12 Uhr ab 12 Uhr Berlin Näh’n’Nerdcafe im Vetomat ab ca. 13:00 ab ca. 13:00 ab ca. 13:00 ab ca. 13:00 Berlin nGbK ab 11:00 ab 11:00 – – Bielefeld Hackerspace Bielefeld ab 13:37 ab 13:37 ab 13:37 ab 13:37 Bremen CCC HB ab 13:37 ab 13:37 ab 13:37 ab 13:37 Burkhardtsdorf Netz09 ab...A Quarter Century After Cyberselfish, Big Tech Proves Borsook Right
In her book Cyberselfish: A Critical Romp Through the Terribly Libertarian Culture of Silicon Valley, published in 2000, Borsook who is based in Palo Alto, California and has previously written for Wired and a host of other industry publications, took aim at what she saw as disturbing trends among the tech industry.
The post A Quarter Century After Cyberselfish, Big Tech Proves Borsook Right appeared first on Purism.
TP-Link Tapo C200: Hardcoded Keys, Buffer Overflows and Privacy in the Era of AI Assisted Reverse Engineering
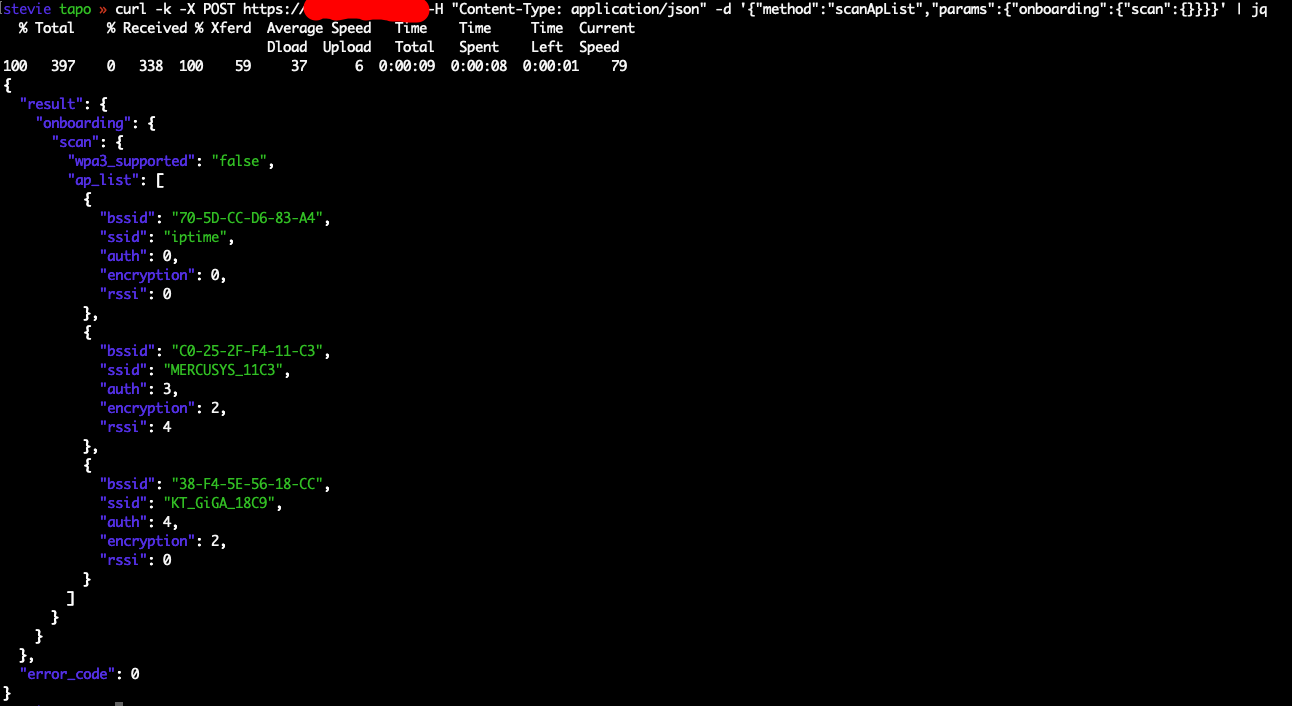
Hi friends and welcome to the last post for this year! Whenever someone asks me how to get started with reverse engineering, I always give the same advice: buy the cheapest IP camera you can find. These devices are self-contained little ecosystems - they have firmware you can extract, network protocols you can sniff, and mobile apps you can decompile. Chances are, you’ll find something interesting. At worst, you’ll learn a lot about assembly and embedded systems. At best, you’ll find some juicy vulnerability and maybe learn how to exploit it!
I own several TP-Link Tapo C200 cameras myself. They’re cheap...
Кросс-трекеры: ретро-музыка на современном ПК

Я не раз обращался к теме музыкальных редакторов системы «трекер». Казалось бы, сколько можно, горшочек, не вари. Но этих программ насчитывается сотни, и несмотря на сходство до степени смешения, созданы они с разными намерениями, посвящены решению различных задач, а к их появлению привели исторические причины разной степени занимательности. В то же время, эта нишевая тема, развивавшаяся десятилетиями, почти не имела выхода за пределы специализированных сообществ в формате обзорных публикаций для массового читателя. А значит, можно и нужно продолжать её раскрывать.
Сегодня уделю пристальное внимание явлению «кросс-трекеров» — программ для современных ПК и операционных систем типа Windows и Linux, позволяющих создавать музыку...