Feed cleverhans-blog [copy] http://www.cleverhans.io/feed.xml has loading error: cURL error 22: The requested URL returned error: 404
Feed Security (b)log [copy] http://securityblogru.livejournal.com/data/rss has loading error: cURL error 22: The requested URL returned error: 403 Forbidden
Feed [bodyawm] Богдан [copy] https://habr.com/ru/rss/users/bodyawm/articles/?fl=ru has loading error: cURL error 22: The requested URL returned error: 404
Second GNUnet Hacker Meeting 2018
Second GNUnet Hacker Meeting 2018 at La Décentrale, Switzerland
The GNUnet hackers met for the second time this year. The primary goal was to squash bugs to bring out a new release. Aside from this we worked hard on improving the documentation and to launch this new website.
Introducing graphene-ng: running arbitrary payloads in SGX enclaves
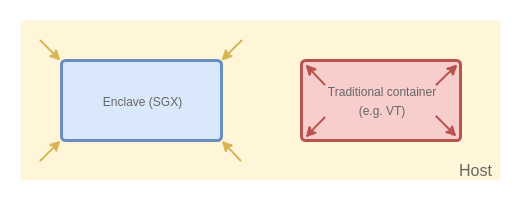
A few months ago, during my keynote at Black Hat Europe, I was discussing how we should be limiting the amount of trust when building computer systems. Recently, a new technology from Intel has been gaining popularity among both developers and researchers, a technology which promises a big step towards such trust-minimizing systems. I’m talking about Intel SGX, of course.
Intel SGX caught my attention for the first time about 5 years ago, a little while before Intel has officially added information about it to the official Software Developer’s Manual. I’ve written two posts about my thoughts on this (then-upcoming) technology, which were a superposition of both positive and negative...
GNUnet 0.11.0pre66
GNUnet 0.11.0pre66
We are pleased to announce the release of GNUnet 0.11.0pre66.
This is a pre-release to assist developers and downstream packagers to test the package before the final release after four years of development.
In terms of usability, users should be aware that there are still a very large number of known open issues in particular with respect to ease of use, but also some critical privacy issues especially for mobile users. Also, the nascent network is tiny (~200 peers) and thus unlikely to provide good anonymity or extensive...
Go Is Amazing, So Here's What I Don't Like About It
https://giphy.com/embed/12NUbkX6p4xOO4

After my last post and generally the kind of indirect advertising I’m doing to the Go programming language for a few months now, I heard about and talked with a lot of people who started being interested in the language, so for once I decided to write what I don’t like about it instead, to provide a more balanced perspective of what’s my experience so far and maybe let some of those people realize that Go is not the right choice for their projects after all.
NOTE 1
It’s important to say that some, if not most of the things I’m about...
All Hail Bettercap 2.0, One Tool to Rule Them All.

It’s with immense pleasure that I announce the release of the second generation of bettercap, a complete reimplementation of the most complete and advanced Man-in-the-Middle attack framework. This release not only brings MITM attacks to the next level, but it aims to be the reference framework for network monitoring (we <3 blueteams too), 802.11, BLE attacks and more! :D
ベッターキャップ!The first thing I want to mention is the amazing team that helped me debugging during endless sessions on Windows, or implemented new features that changed the tool radically, or tested, or gave ideas, or reported bugs (on GitHub, not on Twitter...
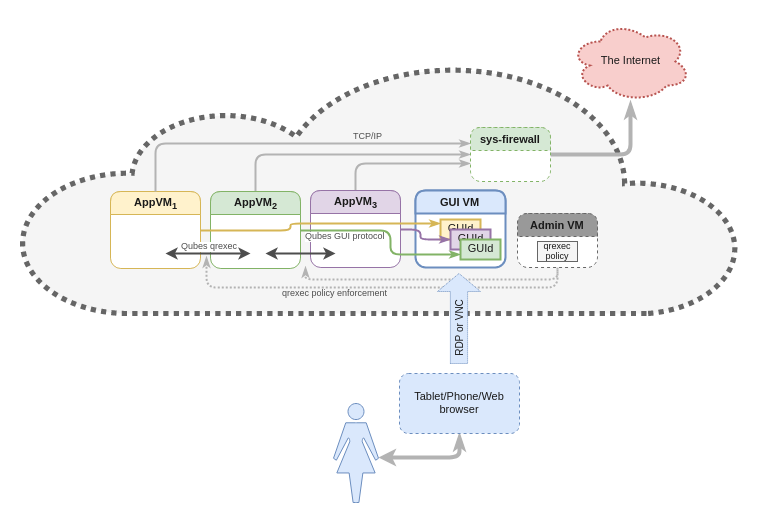
Qubes Air: Generalizing the Qubes Architecture
The Qubes OS project has been around for nearly 8 years now, since its original announcement back in April 2010 (and the actual origin date can be traced back to November 11th, 2009, when an initial email introducing this project was sent within ITL internally). Over these years Qubes has achieved reasonable success: according to our estimates, it has nearly 30k regular users. This could even be considered a great success given that 1) it is a new operating system, rather than an application that can be installed in the user’s favorite OS; 2) it has introduced a (radically?) new approach to managing one’s digital life (i.e. an...
DIY Portable Secrets Manager With a Raspberry Pi Zero and ARC

For the last few days I’ve been working on a new project which I developed for very specific needs and reasons:
I need to store safely (encrypted) my passwords, sensitive files, notes, etc.I need to access them from anywhere, with every possible device ( desktop, mobile, terminal ).I need those objects to be syncronized accros all my devices.I don’t want to use “the cloud”.I don’t want to pay for a server.I don’t want to enable port forwarding and host it myself with DynDNS or alikes.So I wrote ARC.
Of course there are plenty of solutions already that mostly involve the use of...
Объем утечек персональных и финансовых данных за первое полугодие 2017 вырос...в 8 раз.

Мы стараемся "держать руку на пульсе" и делаем регулярные "замеры" объемов утечек в нашей стране и в мире.
Аналитики InfoWatch готовят свежий отчет каждые полгода.
Новая аналитика за первое полугодие 2017 заслуживает внимания хотя бы одной причине: объем утечек персональных и финансовых данных вырос...в восемь раз с 1,06 млрд до 7,78 млрд записей. Напомним, что общий объем скомпрометированной в 2016 году информации в мире составлял всего около трех миллиардов записей.
Резкое увеличение объема потерянной чувствительной информации в первом полугодии 2017 года произошло в результате 20 мега-утечек (от 10 млн записей), на которые пришлось 98% пострадавших записей ПДн и финансовых данных. По...
Introducing the Next Generation Qubes Core Stack
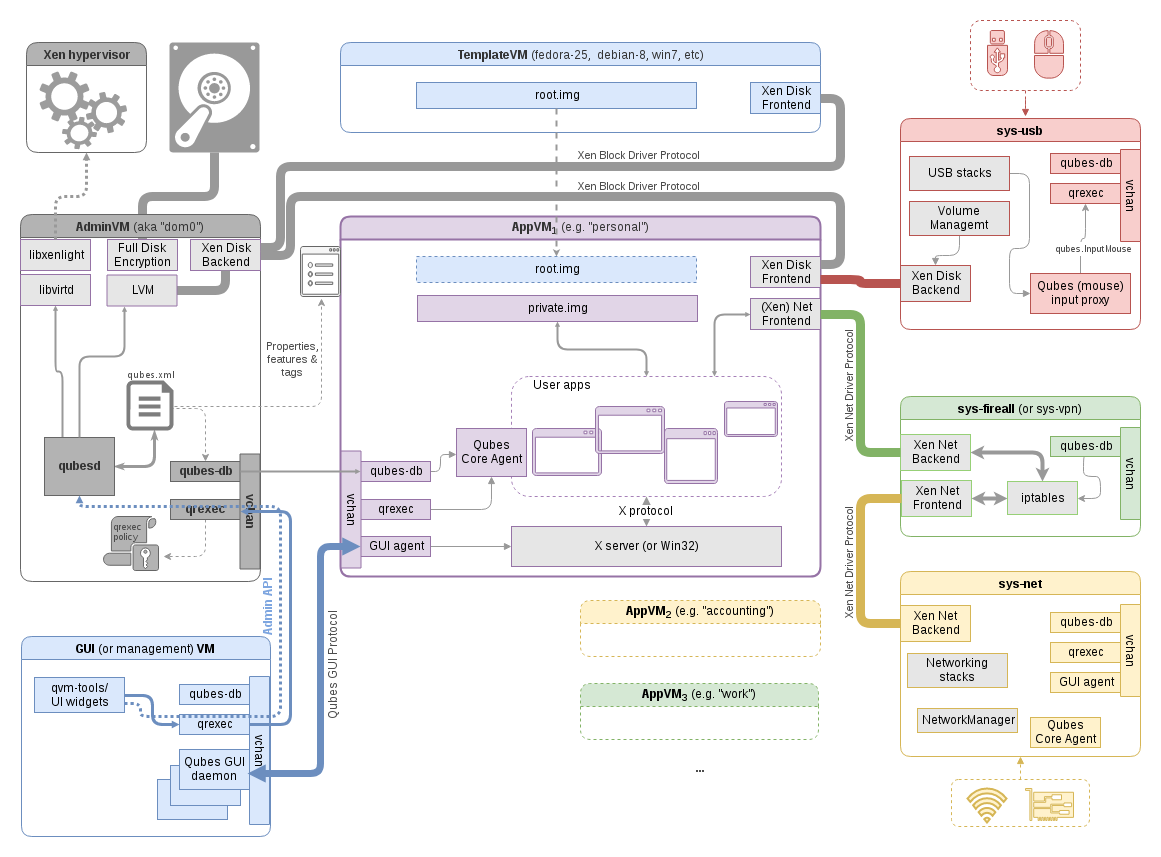
This is the 2nd post from the “cool things coming in Qubes 4.0” series, and it discusses the next generation Qubes Core Stack version 3, which is the heart of the new Qubes 4.x releases. The previous part discussed the Admin API which we also introduced in Qubes 4.0 and which heavily relies on this new Qubes Core Stack.
Qubes Core Stack vs. Qubes OSQubes Core Stack is, as the name implies, the core component of Qubes OS. It’s the glue that connects all the other components together, and which allows users and admins to interact with and configure the system. For the record, the other components of...
This Is Not a Post About BLE, Introducing BLEAH
https://invidious.privacyredirect.com/watch?v=qbmWs6Jf5dc
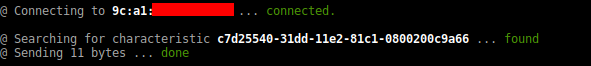
This is not a post about BLE, but rather on how to hack it … well, to be honest, BLE devices are usually very easy to hack, so it’s just a quick intro to it, I’ll also take the chance to open source one of the last tools I’ve made and that I kept private so far. I moved the features I thought to be dangerous ( aka: auto fuzzing all the BLE things and bring chaos ) in a private fork which will stay private, however it’s not that complicated to chain bleah with other tools ( cough …...